Major Security Flaws in LLM Routers Expose Cryptocurrency Wallets to Theft, Researchers Warn
April 13, 2026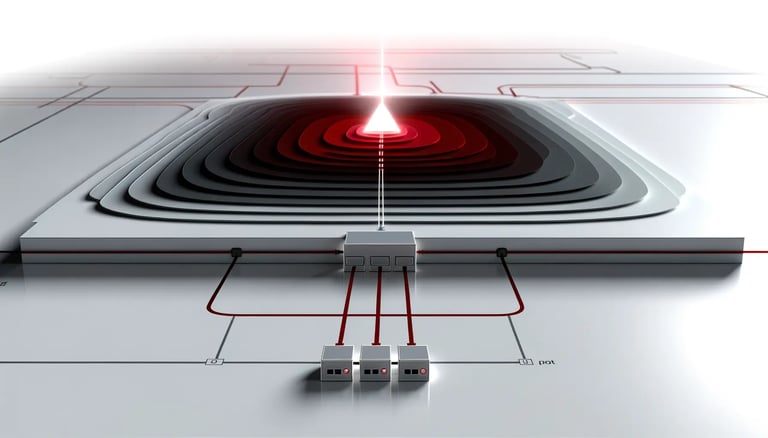
The study shows LLM routers have full access to passing data and can inject malicious commands, exfiltrate credentials, or redirect traffic, risking private keys, API credentials, and wallet access tokens.
In concrete tests, at least one router drained ETH from a researcher’s wallet, and the team warns attackers could poison router traffic to take over hundreds of hosts within hours.
The paper contrasts optimistic industry forecasts for AI agents handling crypto with the lack of guarantees that intermediary infrastructure remains tamper-proof.
The findings come from an arXiv preprint released in April 2026 and have not yet undergone formal peer review; while methodology is rigorous and results plausible, they are unverified.
Security recommendations include never transmitting private keys or recovery phrases through AI sessions, deploying cryptographic signatures to verify AI outputs, and using stronger client-side protections.
Researchers advocate cryptographic signing of model responses to verify provenance and prevent tampered instructions from reaching the agent.
Broader implications point to a need for security-focused standards in AI tool usage across sectors relying on AI-assisted development, potentially leading to certification for LLM router security.
The risk stems from intermediaries that terminate encrypted connections and see plaintext traffic, making it hard for users to detect sensitive data exposure.
The attack surface is the intermediary routing layer between an AI agent and the language model, which lacks meaningful security standardization despite its growing role in crypto workflows.
LLM API routing platforms are a critical security boundary that the industry currently treats as trustworthy by default.
An autonomous 'YOLO mode' exists where AI agents execute commands without user confirmation, increasing risk if a router injects malicious responses.
Researchers from a major university exposed critical vulnerabilities in third-party LLM routers that can enable cryptocurrency theft from developer wallets, demonstrated by a live Ethereum transfer during testing.
Summary based on 6 sources
Get a daily email with more AI stories
Sources
Cointelegraph • Apr 13, 2026
AI Routers Can Steal Credentials and Crypto - Research
CoinDesk • Apr 13, 2026
As AI agents scale in crypto, researchers warn of a critical security gap
crypto.news • Apr 13, 2026
UC researchers warn third-Party AI routers are stealing crypto and private keys
Blockonomi • Apr 13, 2026
Dangerous AI Routers Targeting Cryptocurrency Developers: A New Security Threat