Lenovo Webcams Vulnerable to BadUSB Attacks: Major Threat Exposed at DEF CON 33
August 10, 2025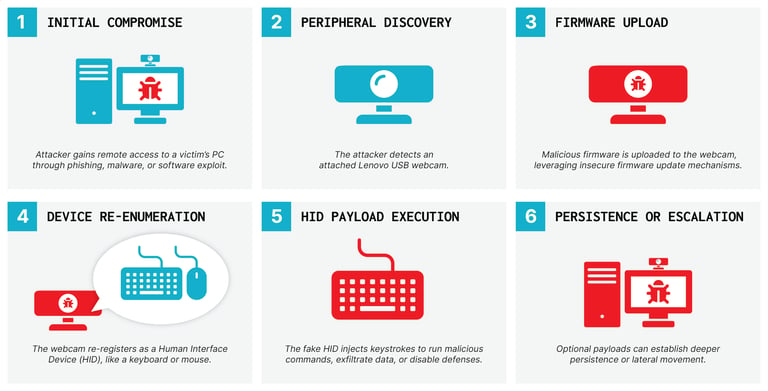
Cybersecurity researchers have identified serious vulnerabilities in certain Lenovo webcams, specifically the 510 FHD and Performance FHD models, that can be exploited for BadUSB attacks, allowing remote attackers to inject keystrokes and launch attacks without needing to access the host operating system.
These vulnerabilities, termed BadCam, enable compromised Linux-based webcams to be remotely hijacked, allowing attackers to reflash firmware and convert these devices into malicious Human Interface Devices (HIDs) without physical access.
BadUSB attacks exploit the inherent trust in USB devices by reprogramming their firmware, which allows them to execute harmful commands on connected computers, effectively bypassing operating system defenses.
The Lenovo webcams were found to have insecure firmware update processes, making them vulnerable to complete software compromise, as attackers can erase and replace the original firmware while maintaining normal functionality.
An attacker could potentially send a backdoored webcam to a victim or connect it physically to compromise a computer, enabling remote commands for post-exploitation activities.
In response to the responsible disclosure of these vulnerabilities, Lenovo has released firmware updates (version 4.8.0) to mitigate the issues and has collaborated with SigmaStar to provide a fix.
Eclypsium has urged Lenovo and SigmaStar to implement firmware verification to prevent such vulnerabilities, and Lenovo has responded by developing an updated installation tool with signature validation.
The findings underscore the urgent need for enhanced security measures, such as firmware signing and device attestation, to protect against sophisticated USB-based attacks in increasingly complex supply chains.
This discovery was presented by principal security researchers Jesse Michael and Mickey Shkatov at DEF CON 33, highlighting a significant security threat in Linux-based USB peripherals.
This marks the first instance where a Linux-based USB peripheral can be weaponized for malicious purposes, demonstrating a significant escalation in cybersecurity threats.
The research highlights a troubling issue: computers often trust their peripherals, which can run their own operating systems and receive remote commands, allowing for potential widespread infection.
The vulnerabilities were revealed during the DEF CON 33 security conference on August 9, 2025, by researchers from Eclypsium.
Summary based on 2 sources
Get a daily email with more Tech stories
Sources

The Hacker News • Aug 9, 2025
Linux-Based Lenovo Webcams’ Flaw Can Be Remotely Exploited for BadUSB Attacks
Security Affairs • Aug 10, 2025
BadCam: Linux-based Lenovo webcam bugs enable BadUSB attacks