Massive Breach Exploits OAuth Tokens, Exposes Critical Flaws in SaaS Security
August 29, 2025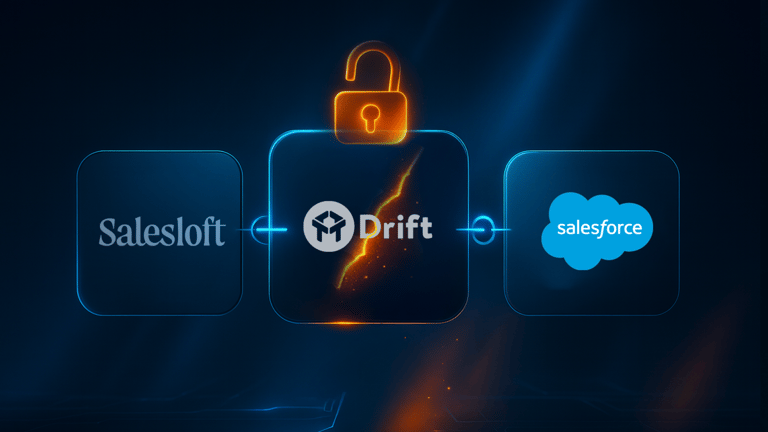
A recent security breach exploited a compromised OAuth token linked to a Drift chatbot integration, which acted as a master key to access multiple Salesforce tenants without the need for phishing or credential theft.
This breach involved the exfiltration of sensitive data from Salesforce instances by bypassing login procedures, multi-factor authentication, and detection systems through the use of these OAuth tokens.
The incident highlights a growing trend where attackers exploit OAuth permissions and trust relationships across SaaS platforms, emphasizing the need for visibility into app-to-app trust chains.
Tools like Grip Security are crucial as they help organizations discover, monitor, and manage SaaS integrations and OAuth risks, providing essential visibility and control to prevent such breaches.
The breach underscores the importance of monitoring OAuth tokens, revoking unused ones, rotating active tokens, and applying least privilege principles to prevent unauthorized access.
This event marks a shift from traditional social engineering attacks to targeting app-to-app trust relationships and OAuth token vulnerabilities, revealing a significant blind spot in SaaS security strategies.
The attack exploited the fact that OAuth tokens often do not expire when employees leave, are not always logged centrally, and can persist for long periods, enabling silent lateral movement within systems.
Summary based on 1 source
Get a daily email with more Tech stories
Source

Security Boulevard • Aug 28, 2025
Inside the Salesloft Breach: A New Era of Salesforce Attacks