Stealthy Cryptojacking Campaign Exploits Pirated Software to Deploy XMRig Miner with Timed Self-Destruct
February 23, 2026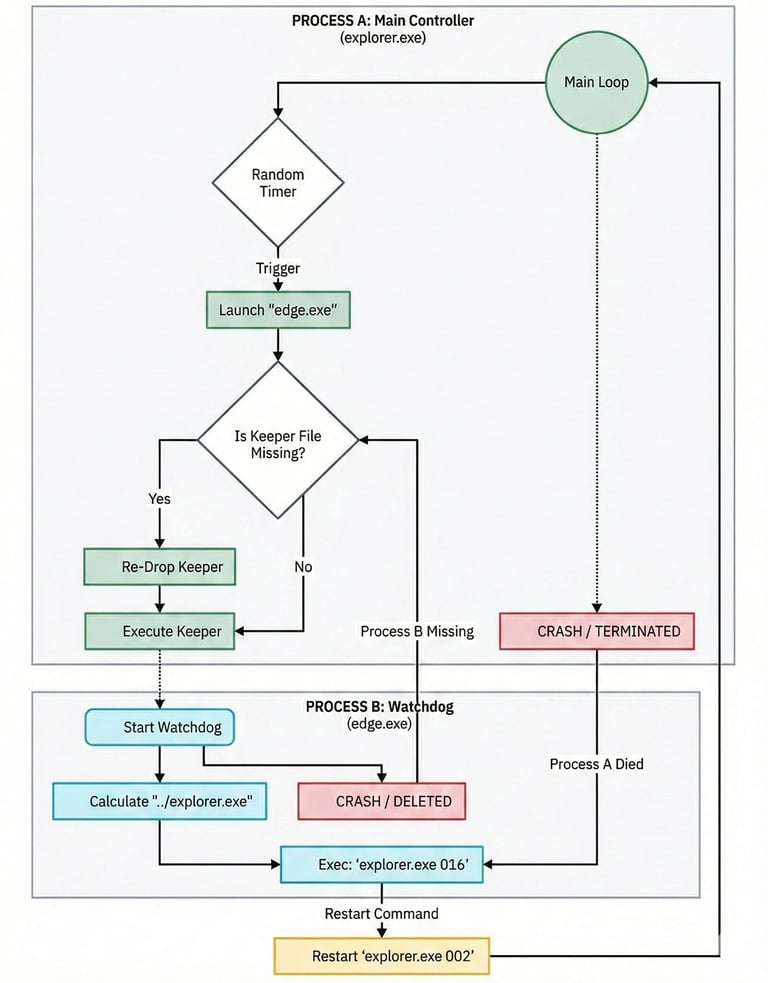
A multi-stage cryptojacking operation uses pirated software bundles as lures to deploy a customized XMRig miner on compromised Windows hosts, with worm-like spread and a modular dropper that acts as installer, watchdog, payload manager, and cleaner.
A hardcoded time-based kill switch triggers a cleanup routine on December 23, 2025, with behavior that shifts before and after this date, suggesting a planned lifecycle ending or transition tied to infrastructure or variant changes.
The core controller binary, Explorer.exe, functions as a persistent state machine that switches roles—installer, watchdog, active infection, and cleanup—based on command-line arguments, enabling multiple operational modes within a single file.
ByOVD technique is used with a legitimate but flawed driver (WinRing0x64.sys) to elevate privileges and boost mining performance, potentially by one-half or more.
Initial infection activity appeared sporadic in November 2025, with a notable spike starting in early December, indicating rollout of new infected nodes or activation of additional components.
The malware exhibits worm-like capabilities, spreading via external storage devices and enabling lateral movement even in air-gapped environments.
Payloads including the miner, watchdogs, and a vulnerable driver are embedded in the binary, decompressed, and written as hidden system files; a circular watchdog relaunches components and can terminate Windows Explorer to disrupt users.
Analysts note AI-assisted malware development and the use of a toolkit to exploit a known vulnerability to distribute XMRig mining payloads.
The dropper is modular, serving as installer, watchdog, payload manager, and cleaner, separating monitoring from mining and persistence components.
A time-based logic bomb installs persistence and starts mining before December 23, 2025, then self-destructs after that date via a specific argument to decommission the infection.
The campaign relies on social engineering to lure users into downloading poisoned installers and uses a circular watchdog topology to maintain persistence.
Overall, the operation represents a sophisticated blend of social engineering, counterfeit software distribution, worm-like propagation, and kernel-level exploits, exposing weaknesses in OS security and signed-driver trust.
Summary based on 2 sources
Get a daily email with more Crypto stories
Sources

The Hacker News • Feb 23, 2026
Wormable XMRig Campaign Uses BYOVD Exploit and Time-Based Logic Bomb
Security Affairs • Feb 23, 2026
Wormable XMRig campaign leverages BYOVD and timed kill switch for stealth