Zig-Compiled Malware Targets Developers with Cross-IDE Infection via Fake GitHub Extensions
April 11, 2026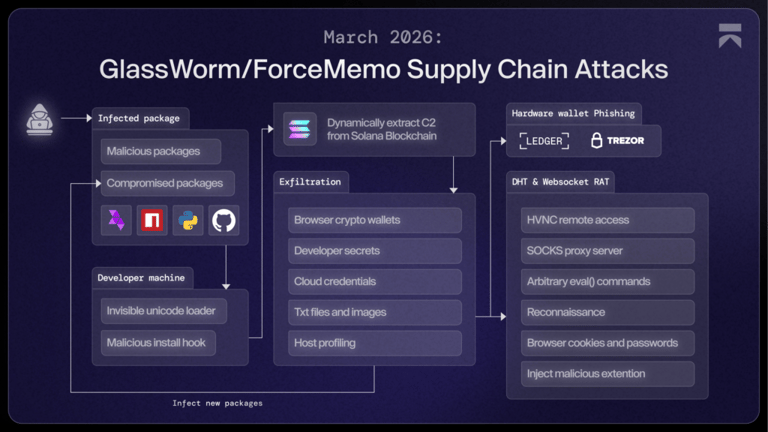
On Windows the binary installs as win.node and on macOS as mac.node (universal Mach-O).
In its latest operation, attackers use a Zig-compiled binary embedded in a malicious OpenVSX extension impersonating WakaTime, with the binary acting as the stealthy dropper rather than the payload.
A Zig-compiled dropper runs outside the JavaScript sandbox with full system access, detects IDEs on the host (including VS Code, Cursor, and VSCodium), downloads a fake extension from GitHub to install across detected IDEs, and then deletes installer traces to stay hidden.
The campaign has been active since 2025 and shows ongoing adaptation to target the developer tooling ecosystem across multiple platforms.
IoCs from Aikido researchers include extensions like specstudio/code-wakatime-activity-tracker and floktokbok.autoimport; affected users should treat systems as compromised and rotate exposed credentials.
The campaign avoids execution on Russian systems and uses the Solana blockchain to fetch commands.
The second stage is the established GlassWorm dropper, which communicates with a Solana-based C2, steals data, and installs a persistent RAT, including a malicious Chrome extension.
The second-stage extension acts as a dropper, communicates with a Solana-based C2, exfiltrates data, and installs a remote access trojan that deploys a Chrome extension for data theft.
The extension ships a Zig-compiled native binary alongside JavaScript, and the binary loads into Node.js at runtime to gain OS-level access.
Experts note this approach bypasses traditional payload delivery by using native, compiled code as an indirection to the GlassWorm dropper, enabling broad cross-IDE compromise.
GlassWorm has evolved into a cross-IDE infection campaign since 2025, moving from malicious npm packages to supply-chain attacks across GitHub, npm, and VS Code, and now deploying RATs via fake browser extensions.
Summary based on 2 sources
Get a daily email with more Tech stories
Sources

The Hacker News • Apr 10, 2026
GlassWorm Campaign Uses Zig Dropper to Infect Multiple Developer IDEs
Security Affairs • Apr 11, 2026
GlassWorm evolves with Zig dropper to infect multiple developer tools