Mirai-Derived Botnet 'xlabs_v1' Exploits Android Devices for Global DDoS Attacks
May 7, 2026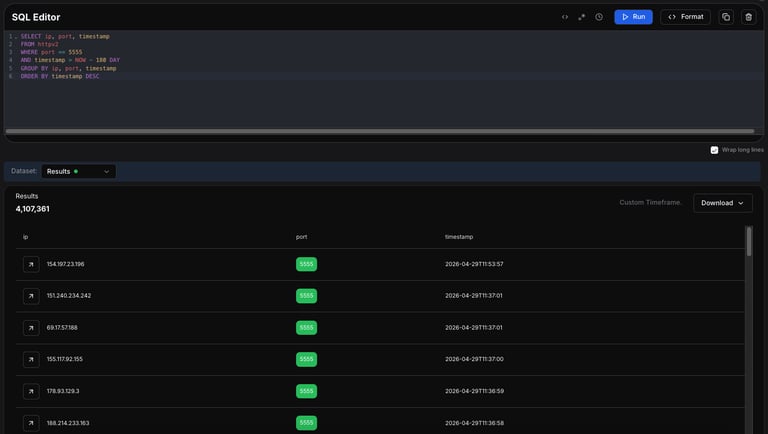
xlabs_v1 is a Mirai-derived botnet that targets devices with exposed Android Debug Bridge (ADB) to orchestrate DDoS attacks, focusing on attackers’ large pool of vulnerable Android devices.
Infection primarily occurs via ADB on TCP/5555, aiming at a global pool of over 4 million targets across Android TV boxes, set-top boxes, smart TVs, routers and other ADB-enabled IoT hardware.
A bandwidth-profiling routine estimates victim bandwidth to price attacks and determine tiered charges, with reinfection necessary due to lack of persistence.
Its infrastructure includes a C2 domain xlabslover.lol resolving to a Netherlands IP, the operator Tadashi, and the xlabs_v1 branding across registrations suggesting planned versioned evolution.
It searches for ADB exposed on TCP port 5555, making Android TVs, set-top boxes, smart TVs, routers and similar IoT gear potential targets.
The C2 uses OpenNIC for resolution with a fallback SOCKS-style listener on TCP/26721, disguising itself as /bin/bash; sensitive strings are ChaCha20-encrypted but recoverable due to key reuse.
The operator uses the alias Tadashi, evidenced by a ChaCha20-encrypted string in builds, though the real actor remains unidentified.
To maximize throughput, the bot opens thousands of parallel sockets, such as 8,192 TCP connections to a nearby Speedtest server, reflecting how pricing tiers are set by measured bandwidth.
The bot supports 21 flood variants across TCP, UDP, and raw protocols, including RakNet and OpenVPN-like UDP, and is marketed as a DDoS-for-hire service targeting game servers and Minecraft hosts.
Contextual assessment notes xlabs_v1 is more sophisticated than typical script-kiddie Mirai forks due to multi-architecture builds, ChaCha20 protection, DNS features and bandwidth profiling, though not matching top-tier TLS-based operations.
The malware includes persistence and evasion features such as self-restart, bandwidth monitoring with 8,192 open sockets, update commands for attacks, and killer functionality to terminate rival malware.
The report situates xlabs_v1 within a broader ecosystem of tooling and actors sharing infrastructure, while confirming xlabs_v1 as a distinct, commercially motivated DDoS platform.
Summary based on 2 sources
Get a daily email with more Tech stories
Sources

The Hacker News • May 6, 2026
Mirai-Based xlabs_v1 Botnet Exploits ADB to Hijack IoT Devices for DDoS Attacks
Security Affairs • May 7, 2026
From Android TVs to routers: the xlabs_v1 Mirai-based botnet built for DDoS attacks