AI-Driven Phishing Attacks Surge, Overtake Vulnerability Exploits as Top Cyber Threat in 2026
April 24, 2026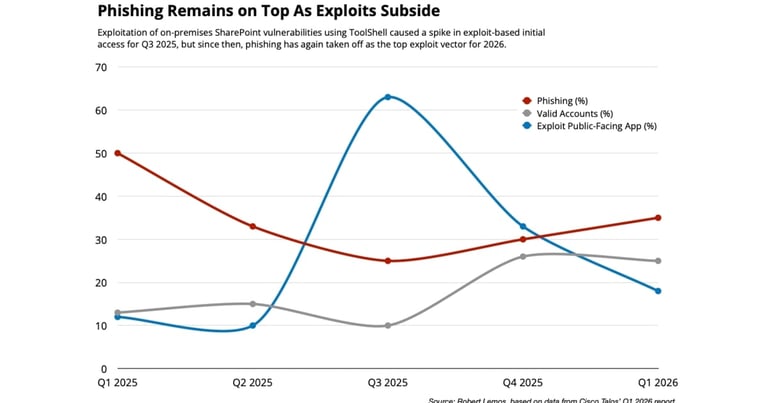
Even with MFA in place, about a third of observed attacks exploit MFA weaknesses, underscoring that MFA should be part of a layered defense rather than the sole protection.
Privileged users—system admins, executives, and accounting staff—are increasingly targeted, making identity-based compromises the dominant pattern in initial access.
In Q1 2026, phishing accounted for 35% of compromises, with attackers leveraging valid accounts in 24% and exploiting public-facing apps in 18% of cases.
AI-assisted phishing shows higher clickthrough rates, with Microsoft reporting a 54% clickthrough compared to an average around 12%.
Phishing has overtaken external vulnerability exploitation as the top initial-access vector in Q1 2026 incident-response engagements, with attackers increasingly using AI to craft convincing phishing emails.
Industry voices from Cisco Talos, Hoxhunt, KnowBe4, and Google Mandiant confirm AI is reshaping attacker capabilities and highlight the need for defensive AI to counteract.
Attackers are abusing legitimate services such as Gmail, Docusign, Outlook, and Salesforce, along with cloud tools, to blur the line between legitimate and malicious activity, aided by domains with DMARC and other authentication techniques.
Experts urge deploying AI defenses and actively hunting for weaknesses, as attackers may use AI to discover and exploit them.
Phishing campaigns have become more diverse in lure content due to AI tooling, now averaging 1.8 emails per campaign rather than large volumes of repetitive messages (polymorphic phishing).
AI-enabled phishing emails are more convincing, multilingual, and harder to detect, enabling broader targeting and personalization.
Summary based on 1 source
Get a daily email with more Tech stories
Source
Dark Reading • Apr 24, 2026
AI Phishing Is No. 1 With a Bullet for Cyberattackers